New Cryptojacking Campaign Compromises Over 3,500 Websites
A new cryptojacking attack campaign has recently emerged, compromising more than 3,500 websites worldwide. This resurgence highlights a concerning trend in browser-based cryptojacking that echoes the infamous operations initiated by platforms like CoinHive in previous years.
What is Cryptojacking?
Cryptojacking involves unauthorized use of a person’s computer to mine cryptocurrency. Attackers embed mining scripts in compromised web pages, enabling them to use the visitor’s CPU to mine coins without their consent. The significant issue here is the potential for increased website loading times and degraded computer performance.
The Latest Findings
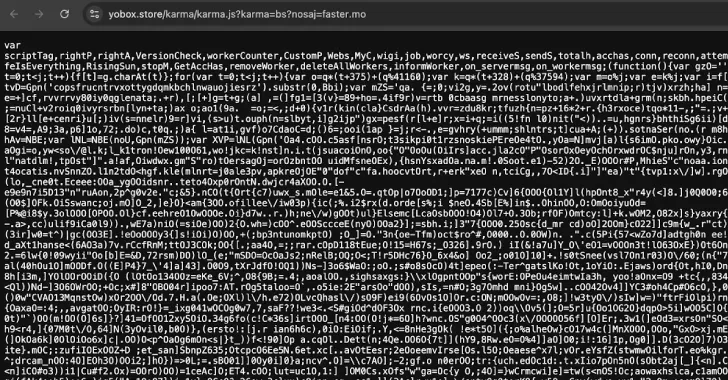
Researchers from c/side have unveiled a sophisticated JavaScript cryptocurrency miner concealed within obfuscated code. This miner assesses the computational power of a user’s device and runs multiple background Web Workers to perform mining tasks simultaneously without raising red flags.
What makes this attack especially adept is its use of WebSockets to fetch mining tasks from an external server. By dynamically adjusting the mining intensity to fit the device’s capabilities, the malicious miner can minimize its resource consumption and maintain a low profile.
“This was a stealth miner, designed to avoid detection by staying below the radar of both users and security tools,” security researcher Himanshu Anand explained.
The Impact on Users
The result of such stealthy operations means that unsuspecting users could be unknowingly mining cryptocurrency while visiting compromised websites. The exact methods by which these websites are breached to facilitate in-browser mining are still under investigation.
To date, it has been confirmed that over 3,500 websites have fallen victim to this broad underground mining initiative. Disturbingly, the domain responsible for hosting the JavaScript miner has also been linked to Magecart credit card skimmers, suggesting that the attackers are diversifying their operations to maximize revenue streams.
Exploiting JavaScript for Dual-Purpose Attacks
This dual-purpose strategy — using the same domain to deliver both mining scripts and credit/debit card exfiltration scripts — reveals the attackers’ capability to weaponize JavaScript for opportunistic attacks on unsuspecting site visitors.
“Attackers now prioritize stealth over brute-force resource theft, using obfuscation, WebSockets, and infrastructure reuse to remain hidden,” c/side noted. “The goal isn’t to drain devices instantly; instead, it is to persistently siphon resources over time, like a digital vampire.”
Additional Threats on the Rise
These findings coincide with ongoing campaigns, including a recent Magecart skimming operation that targets East Asian e-commerce websites. Attackers inject fake payment forms during checkout, siphoning financial information such as bank details from victims. The captured information is subsequently exfiltrated to the attackers’ servers, heightening the risk for individuals and businesses alike.
Varied Methods of Attack
In recent weeks, a range of attacks on client-side and website-oriented systems have been documented, including:
- Incorporating JavaScript embeds that misuse the callback parameter linked to a legitimate Google OAuth endpoint to redirect users to an obfuscated JavaScript payload. This payload sets up a malicious WebSocket connection to an attacker-controlled domain.
- Using Google Tag Manager (GTM) scripts injected directly into the WordPress database to load remote JavaScript that redirects visitors to spam domains.
- Compromising a WordPress site’s wp-settings.php file to include a malicious PHP script that connects to a command-and-control server, leveraging the site’s search engine rankings to inject spammy content.
- Injecting malicious code into a WordPress theme’s footer PHP script to execute browser redirects.
- Using a fake WordPress plugin named after the infected domain to evade detection, activating only when search engine crawlers are detected to serve spam content.
- Distributing backdoored versions of the popular WordPress plugin Gravity Forms through supply chain attacks, allowing attackers to initiate a back door into the admin area of the website.
Consequences of Infection
If malicious code is successfully executed, it will block update attempts for the package and reach out to an external server for additional payload downloads. Such actions render the website vulnerable to a plethora of malicious activities, which include:
- Expansion of remote access.
- Unauthorized arbitrary code injections.
- Manipulating existing admin accounts to consolidate control.
- Access to sensitive stored data within WordPress installations.
In response to these threats, RocketGenius, the team behind Gravity Forms, stated that they are actively working on addressing these vulnerabilities.
Final Thoughts
The resurgence of cryptojacking and other malicious web threats signifies a pressing need for website owners and users alike to remain vigilant. Regular updates, robust security practices, and user education about suspicious activity can help mitigate the risks posed by such sophisticated attacks. The landscape of web security is constantly changing, and awareness is the first step in protecting one’s digital assets.
Explore More:
Latest Bitcoin News |